QED.pl » Case studies » Security on Demand
Security On-Demand (SOD) a well-known network security company provides hundreds of companies and public institutions with advanced cyber threat detection services. SOD’s services include 24/7 threat monitoring and detection, intrusion prevention, automated remediation, and log analysis.
Security On-Demand, wanted to enhance its ability to detect suspicious network events using network traffic data. Their main goal was to strengthen support for Security Operations Centre staff in continuously monitoring the security status of their customers.


The task was to create a system that uses artificial intelligence to select events from logs, which should be dealt with in the first place by Security Operations Center (SOC) employees.
With increasing network traffic and evolving cyber threats, manual monitoring has become cumbersome and difficult. There was an urgent need to develop an advanced and efficient algorithm to automate and improve threat detection rates.
QED Software came up with an innovative approach: crowdsourcing algorithm. Instead of developing the algorithm internally, the collective intelligence of the community was used. The client only had to provide input.
QED Software took control of formally defining the problem, pre-processing the data, preparing the benchmarks and evaluators and promoting the competition. In addition, it oversaw the running of the competition and concluded with a concluding conference session to discuss the results.
An elite algorithm emerged from the multitude of entries, which was then used for further optimisation.
The competition saw the active participation of 250 teams offering their unique solutions. Not only were cash prizes awarded, but also the opportunity to attend the IEEE Big Data conference in Los Angeles and the opportunity to publish at the conference.
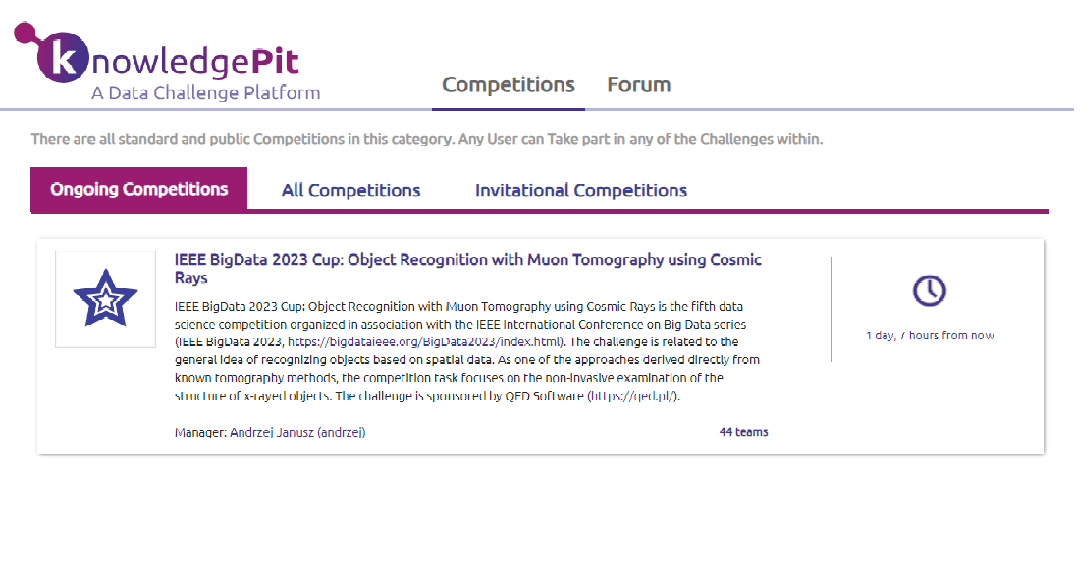

QED Software used its own KnowledgePit.ml competition platform – a platform on which it has been successfully organising similar challenges for years.
An elite algorithm emerged from the competition
The algorithm has been optimised for efficiency. It now serves as one of the core tools for Security On-Demand, helping further refinement and development by their internal teams.
Data science competitions platform knowledgepit.ai
Active learning on tabular data, data labeling optimization,
AI for PIONEERS
Grow your business with artificial intelligence